HowTo Setup A Wireless Notebook With Multiple Network Interface Adapters Using: "nstnetcfg": Difference between revisions
| Line 183: | Line 183: | ||
== NetworkManager Command Line Status == | == NetworkManager Command Line Status == | ||
The output below show the '''NetworkManager'' device status using the command line utility: "'''nmcli'''" | The output below show the '''NetworkManager''' device status using the command line utility: "'''nmcli'''" | ||
<div class="screen"> | <div class="screen"> | ||
Revision as of 10:54, 7 May 2013
Overview

SVN: 4575
This page demonstrates how to setup networking with an NST wireless notebook that is configured with multiple network interface adapters for performing simultaneous network computing surveillance tasks. The NST script: "nstnetcfg" command line software utility was designed to make this task easy to accomplish using a combination of both the "NetworkManager" and "network" services.
The diagram below will be used as a reference for setting up a wireless notebook configured with multiple network interface adapters using NST. The notebook is shown with USB 3.0 Gigabit NIC attachments to the network infrastructure for security tasks and the wireless interface used for management connectivity. This configuration is typical for a Network Security Professional to perform mobile network surveillance tasks and penetration analysis tests.
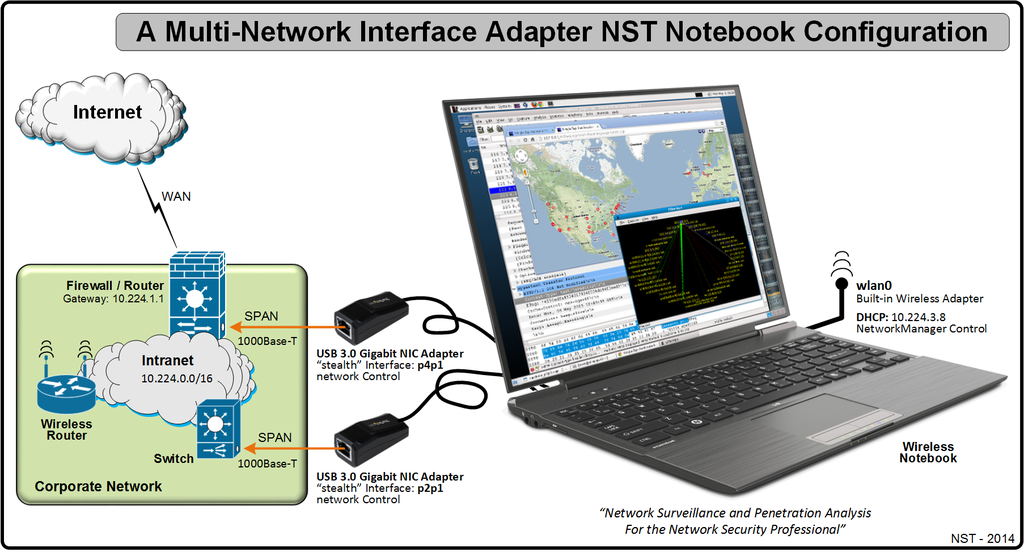
Network Interface Setup Configuration Information
In this section we will identify each network interface and how it should be setup using the "Wireless Notebook" configuration illustrated in the reference diagram above. The NetworkManager service by default will use "DHCP" to derive its network parameters (i.e., IPv4 Adress, Subnet Mask, Host Name, Gateway Address, Name Servers, Time Servers, etc...) The table below depicts values that will be used by the nstnetcfg script.
| Interface / Parameter | Configuration Values | Network Service Management |
|---|---|---|
| wlan0 | Network parameters derived from: DHCP | NetworkManager |
| p2p1 | IPv4 Address: stealth | network |
| p4p1 | IPv4 Address: stealth | network |
Network Interface Configuration: nstnetcfg
The NST script: "nstnetcfg" will now be used for setting up networking on this notebook. This script will enable the "NetworkManager" service for the wireless adapter: "wlan0" and enable the "network" service for "stealth" interfaces: "p2p1" and "p4p1". Use the sequence of nstnetcfg invocations below to serve as an example for setting up networking on your particular wireless notebook with NST.
![]() The "nstnetcfg" script should only be run on a Serial Console or a Desktop Terminal due to the fact that the "IPv4 Address" for this NST system will most likely change.
The "nstnetcfg" script should only be run on a Serial Console or a Desktop Terminal due to the fact that the "IPv4 Address" for this NST system will most likely change.
Initialize All Network Interfaces
The nstnetcfg mode: --init will put the networking setup posture in a known initialized state. Both the "NetworkManager" service and the "network" service will be disabled with their associated configuration files and/or entries removed. The "LoopBack" interface device is never altered or removed with this mode. The Name Service Switch configuration file: "/etc/nsswitch.conf" will have its hosts entry set to: "files dns". It is wise to first use this mode prior to setting up networking so that any lingering "NetworkManager" configuration files will Not interfere with the "network" service operation.
"NetworkManager Service" Configured Interface
The example NST notebook shown above uses the wireless network interface: "wlan0" for network connectivity to and from this NST system.
Interface: wlan0
The configuration for this interface is shown below. Once the "wlan0" network interface is under the control of the NetworkManager service, One will need configure the wireless interface using the NetworkManager applet located on your Desktop.
Stealth Configured Interfaces
The "Stealth" network interfaces (i.e., An interface in the "UP" state with No binding IPv4 Address) will now be configured using the network service. These interfaces are strategically network attached throughout the network infrastructure for surveillance monitoring.
Interface: p2p1
This network interface: "p2p1" is used to monitor specific "Intranet" traffic on a SPAN (Switched Port Analyzer) port.
Interface: p4p1
This network interface: "p4p1" is used to monitor specific "Firewall" traffic on a SPAN (Switched Port Analyzer) port.
Stealth Interface Combo Setting Command
The output below is a compact way of using a Bash "for loop " statement to configure all "Stealth" interfaces in one command line invocation.
Using A Bash Script With "nstnetcfg"
It may be better to use a Bash script given the numerous invocations of "nstnetcfg" with this NST network configuration setup. A good location to store your script would be in directory: "/etc/nst". This will allow one to easily make changes to your network configuration by editing the script and running it. An example script below is shown for: "/etc/nst/net_cfg2.sh" using the above invocations of "nstnetcfg". One can copy and paste this script as a starter template file for your usage.
#!/bin/bash
#
# Script: "net_cfg2.sh"
#
# Description: Helper script for setting up the configuration of network interfaces
# on a wireless notebook using: "nstnetcfg".
#
# Short Usage: "nstnetcfg"
#
# nstnetcfg [-m|--mode TEXT] [-i|--interface DEVICE]
# [-a|--ipv4-addr-prefix IPv4ADDR/PREFIX] [-g|--gateway IPv4ADDR]
# [--mac-addr MACADDR] [--host-name TEXT] [--domain-name TEXT]
# [--name-servers IPv4ADDRLIST] [--hosts-file-only [true]|false]
# [--virtual-host TEXT] [--server-name TEXT]
# [-h|--help [true]|false] [-H|--help-long [true]|false]
# [-v|--verbose [true]|false] [--version [true]|false]
#
# Available Modes: ipv4, dhcp, ssl, stealth, netmgr, rmint, init, show
#
# Uncomment to enable verbosity
#VERBOSE=" --verbose";
#
# Network Interface: Initialization
/usr/bin/nstnetcfg --mode init${VERBOSE};
#
# Network Interface: wlan0
/usr/bin/nstnetcfg --mode netmgr --interface wlan0${VERBOSE};
#
# Network Interface: p2p1
/usr/bin/nstnetcfg --mode stealth --interface p2p1${VERBOSE};
#
# Network Interface: p4p1
/usr/bin/nstnetcfg --mode stealth --interface p4p1${VERBOSE};
#
# Uncomment for using a Stealth Interface Combo Setting
#for i in p2p1 p4p1;
# do /usr/sbin/nstnetcfg --mode stealth --interface ${i};
#done
Script Invocation
Make sure the script has it's execute permissions set:
Execute the script:
NetworkManager Command Line Status
The output below show the NetworkManager device status using the command line utility: "nmcli"