Tunnelling UDP Traffic Through An SSH Connection
Overview
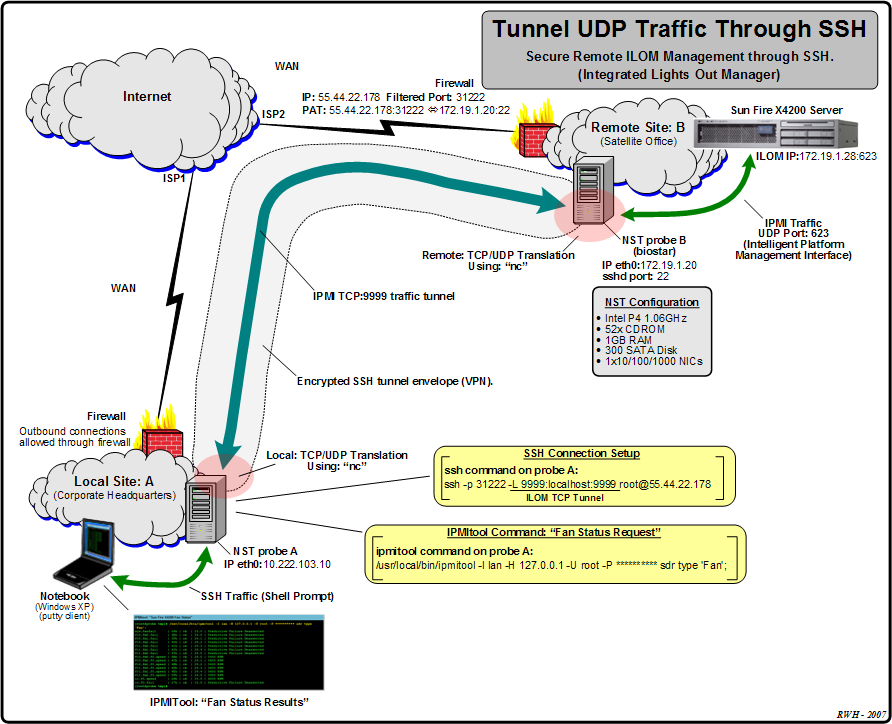
This section describes how to use NST to tunnel a UDP network traffic conversation through an SSH connection. To demonstrate the effective use of UDP tunnelling, we will show how to remotely interrogate a Sun Fire X4200 server's Integrated Lights Out Manager (ILOM) service processor. The command line utility: "IPMItool" generates (UDP Port: "623") (IPMI - Intelligent Platform Management Interface) traffic which will travel through the SSH connection to the remote Sun Fire X4200 server's ILOM service processor network interface.
IPMI over LAN (i.e. a TCP/IP network) uses the Remote Management Control Protocol (RMCP) to support pre-OS and OS-absent management. RMCP is a request-response protocol using UDP datagrams on port: "623".
The network topology below depicts the three systems that are involved, 2 NST probes and one Sun Fire X4200 server. Reference information was taken from: "Performing UDP tunneling through an SSH connection".
Network Topology
Use this network topology as a reference for tunnelling UDP traffic through an SSH connection.
Step By Step Instructions:
Tunnel A TCP Forward Port Through SSH
First we need to establish the tunnel for a "non-used" TCP port from the local NST probe to the remote NST probe SSH server which shares the same LAN as the destination X4200 server.
root@55.44.22.178's password: Last login: Thu Mar 22 11:18:59 2007 from cpe-72-222-76-188.nycaper.res.rdr.com =============================================== = Linux Network Security Toolkit (NST v1.5.0) = ===============================================
In this example SSH traffic is being NATed through a firewall. The SSH filtered port at the dirty side of the firewall is: "31222". We have chosen to use TCP port forwarding for the "non-used" TCP port: "9999". The remote NST probe's IP Address is: "55.44.22.178". On the local NST probe, TCP port: "9999" is bound to the localhost (IP Address: "127.0.0.1").
Use: "nc" To Translate TCP To UDP On The Remote SSH Server Side
On the remote NST probe (SSH server side), we need to open a port listener for TCP port: "9999" and translate all network traffic to UDP port: "623" for the IP Address assigned to the X4200 server's ILOM network interface.
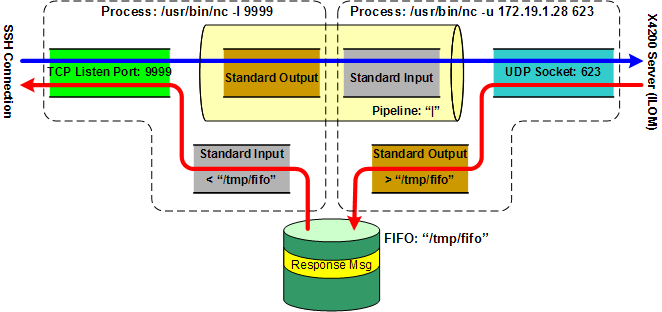
We will first need to create a "fifo". The "fifo" will be necessary to maintain a two-way communication channel between the TCP port listener and the IPMI UDP port. A simple shell pipe would NOT work. It would only communicate left process' standard output to right process' standard input. We will use the Linux command: "mkfifo" to establish the "fifo".
prw-r--r-- 1 root root 0 Mar 22 19:37 /tmp/fifo
Next we will use "nc" (netcat) the "TCP/IP Swiss Army Knife" to perform the TCP/IP to UDP translation.
This command sequence will allow all TCP traffic on the remote NST probe for port: "9999" to be forwarded using the UDP network protocol to the X4200 server's ILOM network interface: 172.19.1.28, UDP port: "623" and receive network traffic responses back.
The diagram below is used to graphically demonstrate the two-way conversation flow at the remote NST probe using the "fifo" and TCP/UDP conversion using: "nc".
Use: "nc" To Translate UDP To TCP On The Local Side
Once again we will need to create a "fifo" and use the "nc" networking utility for protocol translation. The following output shows the "fifo" creation on the local side where we will run the "IPMItool" command.
prw-r--r-- 1 root root 0 Mar 22 19:37 /tmp/fifo
Now perform the UDP to TCP/IP translation using: "nc".
This command sequence will allow all UDP traffic on the local NST probe for port: "623" (the default IPMI UDP port value) to be forwarded using the TCP network protocol to the localhost (IP Address: "127.0.0.1") listening TCP port: "9999" and receive network traffic responses back. The listening TCP IP:Port: "127.0.0.1:9999" was established during the SSH setup above.
Using the UDP Tunnel With "IPMItool"
At this point the UDP tunnel is established through the SSH envelope to the remote ILOM on the X4200 server. We will now demonstrate the use of the "IPMItool" by issuing a IPMI "Fan Status" request command through the UDP tunnel on the local NST probe.
sys.fanfail | 04h | ok | 23.0 | Predictive Failure Deasserted ft0.fm0.fail | 3Eh | ok | 29.0 | Predictive Failure Deasserted ft0.fm1.fail | 3Fh | ok | 29.1 | Predictive Failure Deasserted ft0.fm2.fail | 40h | ok | 29.2 | Predictive Failure Deasserted ft1.fm0.fail | 41h | ok | 29.3 | Predictive Failure Deasserted ft1.fm1.fail | 42h | ok | 29.4 | Predictive Failure Deasserted ft1.fm2.fail | 43h | ok | 29.5 | Predictive Failure Deasserted ft0.fm0.f0.speed | 4Ah | ok | 29.0 | 5400 RPM ft0.fm2.f0.speed | 4Ch | ok | 29.1 | 5600 RPM ft0.fm1.f0.speed | 4Bh | ok | 29.2 | 5400 RPM ft1.fm0.f0.speed | 4Dh | ok | 29.3 | 5600 RPM ft1.fm1.f0.speed | 4Eh | ok | 29.4 | 5600 RPM ft1.fm2.f0.speed | 4Fh | ok | 29.5 | 5900 RPM io.f0.speed | 26h | ok | 15.0 | 4200 RPM io.f0.fail | 27h | ok | 15.0 | Predictive Failure Deasserted
The "IPMItool" could also have been run from a browser attached to the NST WUI "IPMItool" management interface page on the local NST probe.
Summary
The IPMI "Fan Status" request initiated at a shell prompt on a local NST probe will be sent to UDP listening port: "127.0.0.1:623" which will then be translated to TCP and forwarded to the TCP listening port: "127.0.0.1:9999". This traffic will be securely tunneled through an SSH connection which travels through a firewall using both NAT (Network Adress Translation) and PAT (Port Address Translation) to a remote NST probe which is also listening on TCP port: "127.0.0.1:9999". The traffic is then translated back to UDP and finally forwarded and to the destination ILOM UDP listening port: "172.19.1.28:623" on the Sun Fire X4200 server. The resultant information is sent in reverse order back as a response to the IPMI "Fan Status" request.
An Alternative Tunnel: VPN - PPP Tunneled Over SSH
Please see the article: "Using VPNs With NST" on how to create alternate secure tunnels using NST and SSH connections.